The Future of Security: Checking Out the Newest Patterns in Electronic Safety Technologies
In the realm of security and protection, the landscape is frequently progressing, driven by technological innovations that push the borders of what is possible. Digital security innovations have actually become significantly advanced, using cutting-edge services to resolve the ever-growing challenges dealt with by individuals and companies alike. From biometric verification to the integration of fabricated intelligence and maker knowing, these fads hold the promise of improving protection measures in unmatched means. As we browse through this complex internet of advancements, one can not help however ask yourself how these innovations will certainly form the future of safety and safety and security, establishing the phase for a brand-new era of security and durability (BQT Locks).
Surge of Biometric Verification
With the enhancing requirement for protected and convenient verification approaches, the surge of biometric verification has transformed the way individuals access and protect their delicate info. Biometric authentication utilizes one-of-a-kind organic attributes such as fingerprints, face attributes, iris patterns, voice recognition, and even behavior characteristics for identification confirmation. This innovation provides an extra trusted and safe and secure technique compared to standard passwords or PINs, as biometric data is unbelievably hard to duplicate or steal.
Among the essential benefits of biometric authentication is its convenience. Customers no more require to bear in mind complex passwords or bother with losing accessibility because of forgotten qualifications. By merely utilizing a part of their body for verification, people can quickly and firmly access their devices, accounts, or physical rooms.
Furthermore, biometric verification improves protection by supplying an extra robust protection versus unauthorized accessibility. With biometric pens being distinct to every person, the risk of identification burglary or unauthorized entrance is significantly minimized. This enhanced level of safety is specifically important in industries such as money, medical care, and government where safeguarding delicate details is critical.
Combination of AI and Equipment Learning
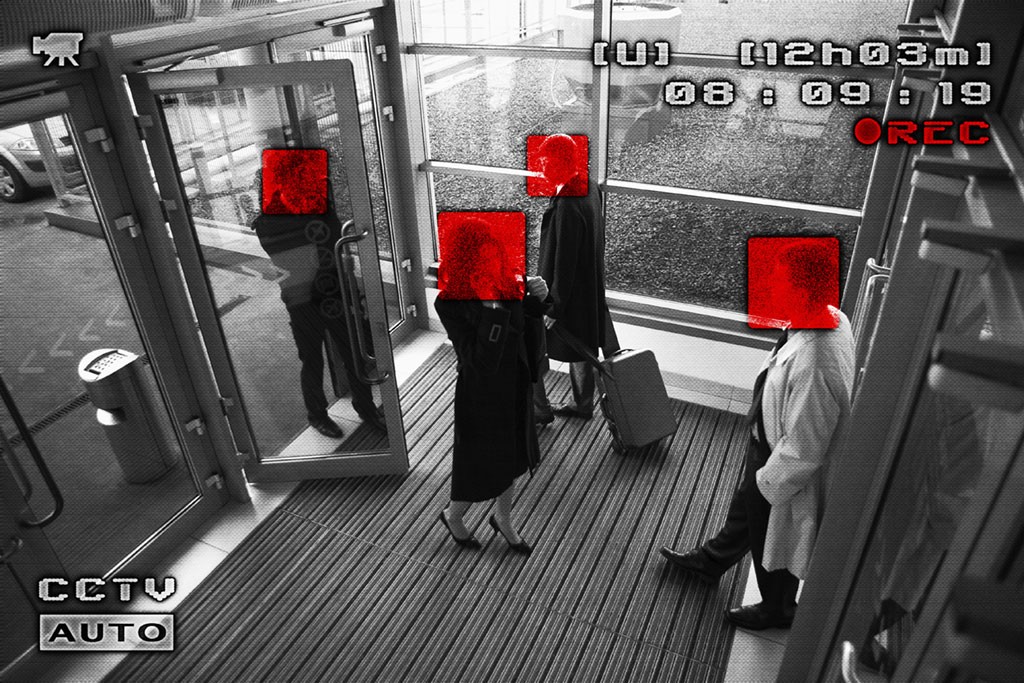
The development of digital protection modern technologies, exhibited by the increase of biometric verification, has actually led the way for advancements in the combination of AI and Equipment Learning for enhanced identification and defense devices. By leveraging AI formulas and Artificial intelligence designs, digital protection systems can currently assess vast quantities of data to spot patterns, abnormalities, and prospective dangers in real-time. These modern technologies can adjust to evolving security threats and provide proactive feedbacks to minimize threats properly.
One significant application of AI and Device Knowing in electronic safety and security is in anticipating analytics, where historic data is used to anticipate possible safety breaches or cyber-attacks. This proactive strategy permits security systems to prepare for and protect against dangers before they occur, boosting general precaution. In addition, AI-powered monitoring systems can intelligently monitor and assess video feeds to recognize dubious tasks or people, improving response times and lowering duds.
IoT and Smart Safety Devices
Advancements in digital security modern technologies have brought about the introduction of Get the facts IoT and Smart Safety and security Instruments, transforming the means protection systems run. The Internet of Points (IoT) has allowed security gadgets to be interconnected and remotely accessible, providing boosted monitoring and control abilities. Smart Protection Gadgets, such as clever cameras, door locks, and movement sensing units, are equipped with performances like real-time signals, two-way communication, and combination with various other smart home systems.
One of the considerable benefits of IoT and Smart Safety Instruments is the capability to give users with seamless accessibility to their protection systems through mobile phones or various other internet-connected tools. This convenience permits remote tracking, equipping, and deactivating of security systems from anywhere, offering house owners with assurance and adaptability. These tools often incorporate advanced functions like facial recognition, geofencing, and activity pattern acknowledgment to improve general protection degrees.
As IoT proceeds to advance, the assimilation of expert system and equipment understanding formulas into Smart Safety and security Tools is anticipated to more boost discovery accuracy and customization options, making digital protection systems much more effective and reputable.
Cloud-Based Safety Solutions
Becoming an essential element of modern digital protection framework, Cloud-Based Safety Solutions use unparalleled adaptability and scalability in guarding electronic assets. By leveraging the power of cloud computer, these options offer organizations with sophisticated safety and security features without the need for considerable on-premises equipment or infrastructure. Cloud-based protection services enable remote surveillance, real-time notifies, and centralized administration of safety and visit site security systems from any type of area with an internet link. This not just improves comfort but also enables for quick actions to security incidents.
Furthermore, cloud-based safety and security solutions offer automated software program updates and upkeep, making sure that safety systems are always up-to-date with the latest defenses against emerging hazards. On the whole, cloud-based safety services stand for an economical and effective way for businesses to boost their safety pose and protect their electronic properties.
Emphasis on Cybersecurity Procedures
With the enhancing sophistication of cyber dangers, companies are positioning a vital focus on strengthening their cybersecurity steps. BQT Biometrics Australia. As innovation advances, so do the approaches employed by cybercriminals to breach systems and take delicate information. This has actually prompted companies to spend heavily in cybersecurity procedures to protect their data, networks, and systems from destructive attacks
One of the key patterns in cybersecurity is the fostering of advanced encryption methods to safeguard data both at remainder and en route. Encryption assists to make certain that even if data is obstructed, it continues to be unreadable and protected. In addition, the execution of multi-factor authentication has actually come to be increasingly common to add an additional layer of security and verify the identifications of users accessing sensitive details.

Verdict